The Cybersecurity and Infrastructure Security Agency (CISA), in collaboration with the Federal Bureau of Investigation (FBI) and the Multi-State Information Sharing and Analysis Center (MS-ISAC), has released a comprehensive guide.
It aimed at assisting federal, state, local, tribal, and territorial government entities in responding to Distributed Denial-of-Service (DDoS) attacks.
Understanding the Threat Landscape
DDoS attacks originate from multiple sources and can be particularly challenging to trace and block.
The guide provides an in-depth overview of the DoS and DDoS landscapes, detailing attack types, motivations, and potential impacts on government operations.
It emphasizes the importance of planning for emerging DDoS trends and technologies to better defend against malicious activity.
CISA and FBI have recently released a comprehensive guide that provides technical details and best practices to respond effectively to Distributed Denial of Service (DDoS) attacks.
Free Webinar : Mitigating Vulnerability & 0-day Threats
Alert Fatigue that helps no one as security teams need to triage 100s of vulnerabilities. :
- The problem of vulnerability fatigue today
- Difference between CVSS-specific vulnerability vs risk-based vulnerability
- Evaluating vulnerabilities based on the business impact/risk
- Automation to reduce alert fatigue and enhance security posture significantly
AcuRisQ, which helps you to quantify risk accurately:
DoS vs. DDoS: What’s the Difference?
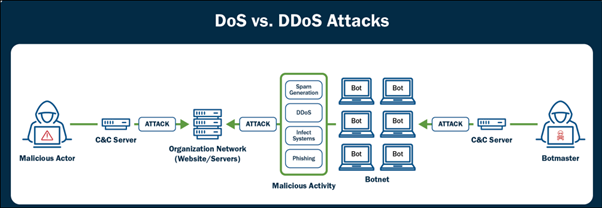
The guide clarifies the distinction between DoS and DDoS attacks.
A DoS attack typically involves a single source overwhelming a system with traffic, while a DDoS attack uses multiple sources, often coordinated through botnets, to amplify the disruption.
The distributed nature of DDoS attacks makes them more challenging to defend against.
CISA Cyber recently tweeted about the release of a guide by CISA and FBI that provides detailed information on how to respond to DDoS attacks
 22 March 2024
22 March 2024